Schedule your FREE demo today!
Schedule a FREE demonstration or ask any question. We’d be happy to help.
[gravityform id="4" title="false" description="false"]eDiscovery Software | eDiscovery Collection Software | Pinpoint Labs
CROSSCOPY ENTERPRISE
For nearly two decades, Pinpoint Labs has built software for legal, corporate, and investigative teams. Our systems are grounded in confidentiality, integrity, and availability; security is foundational, not an afterthought.
Our Security Framework
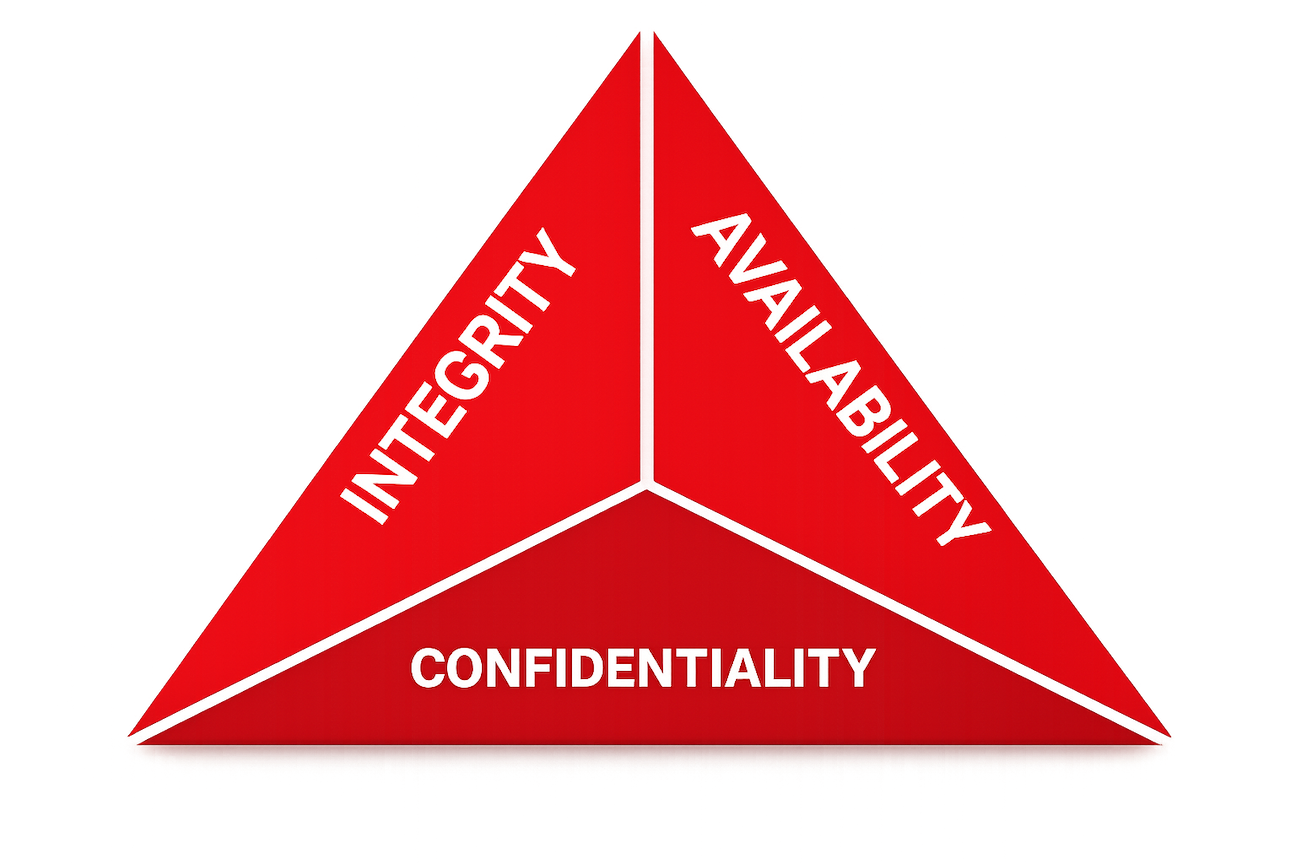
Built on the CIA Triad, the industry standard for information security architecture.
Role-based access, MFA, and least-privilege enforcement ensure only authorized parties reach sensitive data.
Hash-based verification and comprehensive audit trails ensure every collection is tamper-evident and defensible.
Resilient infrastructure and continuous monitoring keep your collection workflows running when it matters most.
Pinpoint Labs maintains a comprehensive security program aligned with internationally recognized standards, independently audited and validated.
International standard for information security management systems — covering risk, governance, access control, and continuous improvement.
Ongoing independent audit confirming operational effectiveness of controls for security, availability, confidentiality, and processing integrity over time.
Pinpoint Labs products are designed for environments where data security and evidentiary integrity are critical. Our architecture minimizes data exposure and reduces risk at every layer.
Security is not a feature layer. It is built into every collection workflow across both CrossCopy products.
CrossCopy Enterprise is a remote collection platform designed for secure, targeted collection of files and communications from enterprise data sources and endpoint devices.
CrossCopy Mobile enables targeted mobile device collections while maintaining strong privacy protections and custodian-controlled review before transfer.
Security is integrated throughout our software development lifecycle, not added at the end.
Every line is reviewed and validated against security standards before reaching production.
We test against real-world attack scenarios using independent experts to validate our security posture.
Our program evolves alongside emerging threats, new technologies, and changing regulatory requirements.
Get In Touch
For questions regarding certifications, practices, or responsible disclosure policies, reach out directly to our security team.
Request Security DocumentationNearly two decades of building software that legal and investigative teams trust with their most sensitive data.
Pinpoint Labs maintains a continuously evolving security program designed to adapt to emerging threats, technologies, and regulatory requirements, so your collections stay defensible today and tomorrow.
← Back to CrossCopy EnterpriseSchedule a FREE demonstration or ask any question. We’d be happy to help.
[gravityform id="4" title="false" description="false"]CrossCopy Mobile makes mobile data collection easy, fast, and secure—whether your custodians are across the hall or across the country. No apps to install. No tech headaches.